Examples Of Election Cyberattacks
Unfortunately, over the past few years, elections in both Europe and the United States faced numerous attacks.
Some recent examples of attempted election attacks include the following:
- In 2015, the European Unions e-voting websites, the Federal Election Commission and the State Registration Service, were targeted by Denial-of-Service attacks concurrently with the start of local elections and referendums.
- In the run-up to the US presidential election in 2016, a wide range of Russians searched for vulnerabilities in state voter databases and hacked the Hillary Clinton campaign, the Democratic Congressional Campaign Committee , and the Democratic National Committee . They also attempted to breach Sen. Marco Rubios campaign and the Republican National Committee. Additionally, politically damaging information was released online and false information was spread via Twitter, Facebook, YouTube, and Instagram.
- In 2018, the US government accused Russian nationals of attempting to tamper with the 2016 presidential election. This represented a shift from detecting and defending malicious activity to directly confronting cyber threats.
Does The Fbi Hire Cybersecurity
FBI Special Agents apply their professional experience and unique skill sets to their work every day. Because technology permeates every aspect of what we do, our Special Agents come from all IT backgrounds: network information, cybersecurity, computer science, digital forensics and other technical specialties.
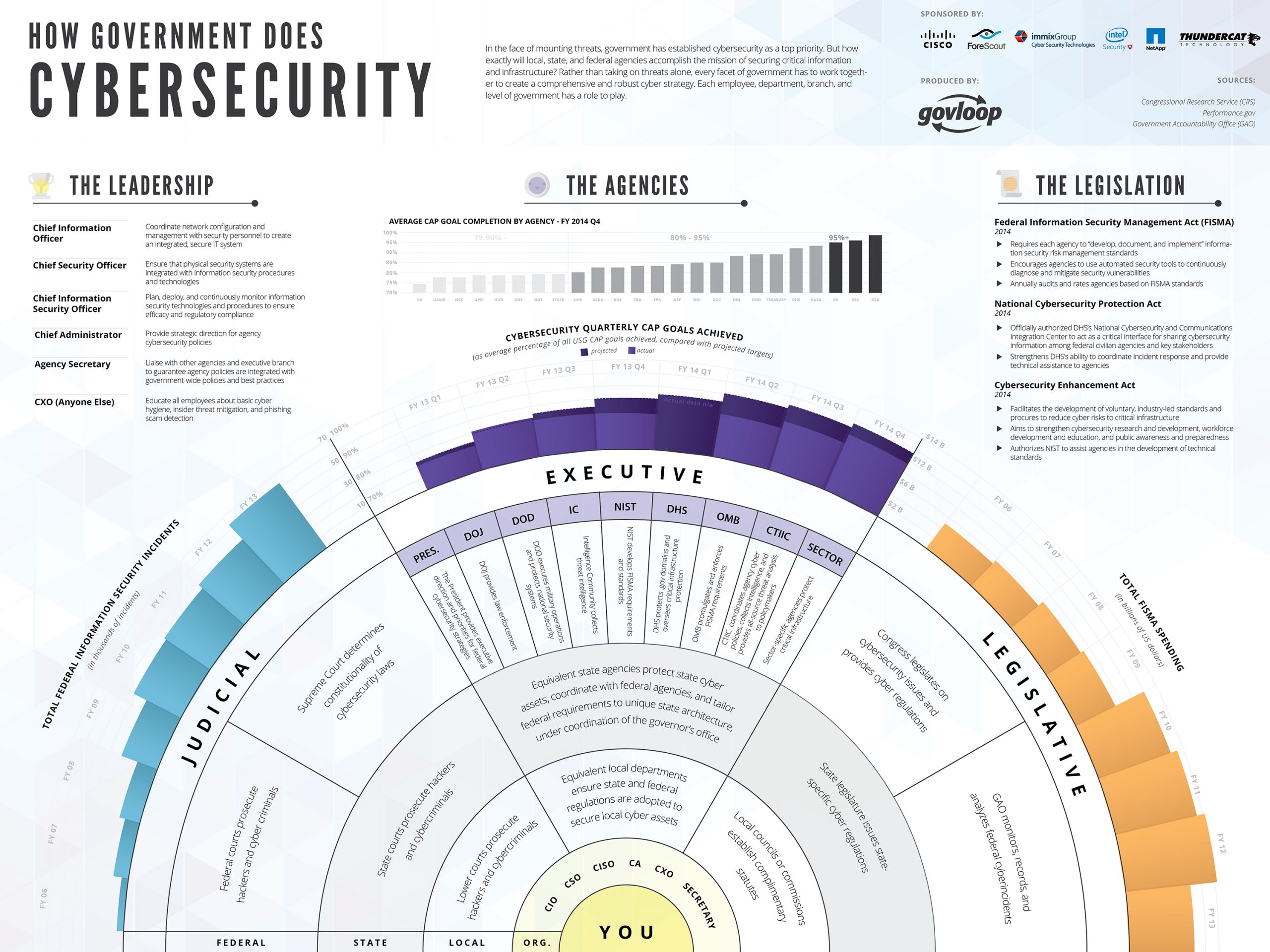
Roles Of Other Government Organizations
- 5.1This section identifies key government organizations in relation to this policy. In and of itself, this section does not confer any authority.
- 5.2This section identifies lead security agencies and/or internal enterprise service organizations that have a leadership and support role in relation to this policy and contribute to the achievement of government security policy objectives. The responsibilities of each organization are identified, in accordance with its mandate, including the principal internal enterprise services provided.
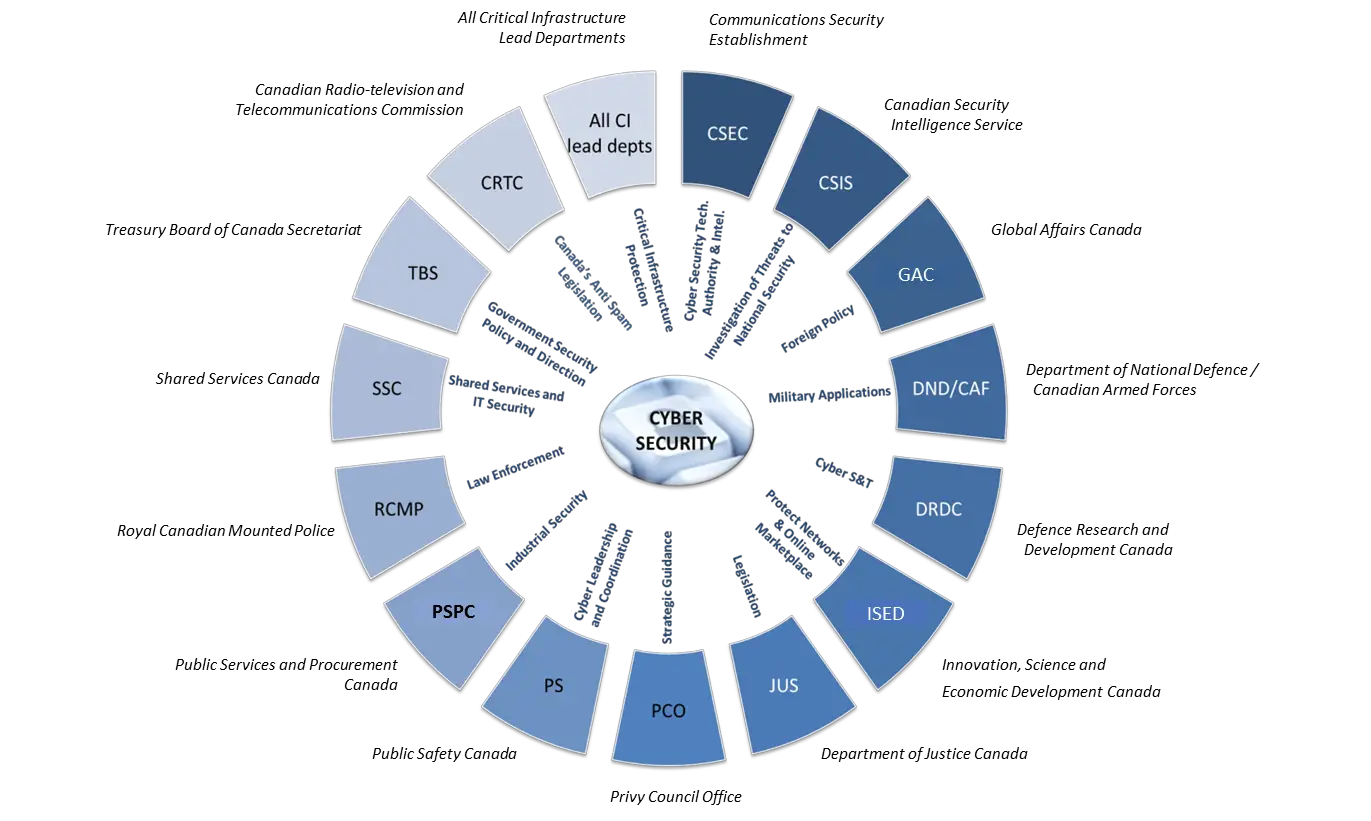
- 5.3The Canadian Security Intelligence Service is responsible for the following:
- 5.3.1Providing government-wide services in security screening
- 5.3.2Fulfilling government-wide functions by investigating and analyzing threats to the security of Canada and by providing related reporting and advice to the Government of Canada and
- 5.3.3Maintaining a central registry for the retention of forms that designate persons permanently bound to secrecy under the Security of Information Act.
You May Like: How Much Can The Government Garnish Your Wages
Why Cyber Security Matters
Canada is one of the most connected countries in the world. We live our lives online, and we need to be able to trust our cyber systems. Digital technologies and the internet are increasingly important to innovation and economic growth. A safe and secure cyber space is important for the security, stability and prosperity of Canada, and good cyber security is critical to Canadas competitiveness, economic stability, and long-term prosperity.
Cyber defence is a team sport. Government, industry, academia, and civil society must all work together to strengthen Canadas cyber security.
Cybersecurity Resources For Small Businesses
The Office of Communications Business Opportunities provides Internet links to information about government agencies and private organizations that have educational resources and tools related to cybersecurity. The descriptions and links below are for informational purposes only. The FCC does not endorse any non-FCC product or service and is not responsible for the content of non-FCC websites, including their accuracy, completeness, or timeliness.
Recommended Reading: Government Fraud Waste And Abuse
Are The Government Corporations And Individuals All Responsible For Cybersecurity
To some degree, everyone is responsible for cybersecurity. Governments have a responsibility to protect their citizens, and in the modern world, that means taking steps to ensure that digital resources are protected from outside interference.
Companies need to keep their customers data safe. At the same time, its important for users of technology to implement cybersecurity measures, such as using decent passwords and avoiding phishing schemes.
While cybersecurity is a complex and ever-evolving process, taking certain precautions can help minimize the risks. And ultimately, the cybersecurity responsibility falls on everyone whether you are a government official, a business CEO, or an average Joe.
National Cyber Security Division
The National Cyber Security Division is a division of the Office of Cyber Security & Communications, within the United States Department of Homeland Securitys Cybersecurity and Infrastructure Security Agency. Formed from the Critical Infrastructure Assurance Office, the National Infrastructure Protection Center, the Federal Computer Incident Response Center, and the National Communications System, NCSD opened on June 6, 2003. The NCSD mission is to collaborate with the private sector, government, military, and intelligence stakeholders to conduct risk assessments and mitigate vulnerabilities and threats to information technology assets and activities affecting the operation of the civilian government and private sector critical cyber infrastructures. NCSD also provides cyber threat and vulnerability analysis, early warning, and incident response assistance for public and private sector constituents. NCSD carries out the majority of DHS responsibilities under the Comprehensive National Cybersecurity Initiative. The FY 2011 budget request for NCSD is $378.744 million and includes 342 federal positions. The current director of the NCSD is John Streufert, former chief information security officer for the United States Department of State, who assumed the position in January 2012.
Read Also: At& t Internet Government Assistance
Cyber Careers Within The Government Of Canada
Cyber security professionals within the government of Canada play a critical role protecting our citizens, economy and democracy.
We are sharing information about this exciting career path, and highlighting career opportunities in the federal government.
Also Check: Congress Mortgage Stimulus For Middle Class
Get Information On Ransomware
Ransomware attacks are increasing in scale, sophistication, and frequency, victimizing governments, individuals, and private companies around the world. The Cybersecurity and Infrastructure Security Agency has launched StopRansomware.gov a one-stop resource for individuals and organizations of all sizes to reduce their risk of ransomware attacks and improve their cybersecurity resilience. This webpage brings together tools and resources from multiple federal government agencies under one online platform. Learn more about how ransomware works, how to protect yourself, how to report an incident, and how to request technical assistance.
Also Check: Government Cng Vehicles For Sale
Resilience Of Democratic Institutions
Fair and free elections are a hallmark of American democracy. The American peoples confidence in the value of their vote is principally reliant on the security and resilience of the infrastructure that makes the Nations elections possible. Accordingly, an electoral process that is both secure and resilient is a vital national interest and one of the Department of Homeland Securitys highest priorities. The Departments Cybersecurity and Infrastructure Security Agency is committed to working collaboratively with those on the front lines of electionsstate and local governments, election officials, federal partners, and vendorsto manage risks to the Nations election infrastructure. CISA will remain transparent and agile in its vigorous efforts to secure Americas election infrastructure from new and evolving threats.
The Importance Of Cyber Technologies In Government
Every day the federal government fends off tens of thousands of cyberattacks from adversaries. Some of these attacks are simple phishing emails aimed at hopefully tricking an unassuming federal employee to more sophisticated attacks targeting the nations most precious data assets.
Protecting federal agencies from cyberattack is not an easy job, but an incredibly important one as more and more information goes digital. When you think about the mission of the federal government, agencies host the personal information of every man, woman and child in the country, financial data, information related to national security and nearly everything in between. The government presents a treasure trove of information that hackers want.
To fight back, government agencies use cybersecurity tools. As the hackers have gotten more sophisticated so have the tools to stop them. Agencies need to protect data at every stage of its life from the moment it is collected, to when it is transmitted, to where it is stored and finally until it is deleted. At the NIH Information Technology Acquisition & Assessment Center, we understand this challenge. More importantly, we understand the technology agencies need in order to keep information secure.
As the federal government has learned in recent years, keeping information secure can be difficult, but failure to do so can be catastrophic.
The OPM Breach
Recommended Reading: Us 10 Year Government Bond Yield
Reporting Cyber Incidents To The Federal Government
Cyber Incident Reporting: A Unified Message for Reporting to the Federal Government
Presidential Policy Directive /PPD-41, United States Cyber Incident Coordination, outlines the roles federal agencies play during a significant cyber incident. The Department of Homeland Security is unique among agencies in that it plays a major role in both asset response and threat response. Asset response focuses on the assets of the victim or potential targets of malicious activity, while threat response includes identifying, pursuing, and disrupting malicious cyber actors and activity.
DHS is the lead agency for asset response during a significant cyber incident. The departments National Cybersecurity and Communications Center assists asset owners in mitigating vulnerabilities, identifies other entities that may be at risk, and shares information across the public and private sectors to protect against similar incidents in the future. The Department of Justice, through the FBI and the NCIJTF, is the lead agency for threat response during a significant incident, with DHSs investigative agenciesthe Secret Service and ICE/HSI playing a crucial role in criminal investigations.
This fact sheet, Cyber Incident Reporting: A Unified Message for Reporting to the Federal Government, explains when, what, and how to report a cyber incident to the federal government.
Cybersecurity For Small Businesses
The Internet allows businesses of all sizes and from any location to reach new and larger markets and provides opportunities to work more efficiently by using computer-based tools. Whether a company is thinking of adopting cloud computing or just using email and maintaining a website, cybersecurity should be a part of the plan. Theft of digital information has become the most commonly reported fraud, surpassing physical theft. Every business that uses the Internet is responsible for creating a culture of security that will enhance business and consumer confidence. In October 2012, the FCC re-launched the Small Biz Cyber Planner 2.0, an online resource to help small businesses create customized cybersecurity plans.
The FCC also released an updated one-page Cybersecurity Tip Sheet. The quick resource features new tips on creating a mobile device action plan and on payment and credit card security.
Read Also: How To Get Off Government Watch List
Does Dhs Deal With Cyber Security
DHS S& T works to strengthen the nation’s cybersecurity with the latest and best innovations by partnering with the private sector to include small businesses, international partners, law enforcement and other first responders, industry and academic groups to develop advanced critical infrastructure and cyber
World’s Leading Companies in the Cybersecurity Market: Top 10 by Revenue
- Cisco Systems, Inc.
Federal Agencies With A Role In Ensuring Enterprise Cybersecurity
As hackers hone their skills, businesses deal with cybersecurity concerns on a daily basis. Most major hacks to date have focused on a specific company or agency. But what if a large cyberattack were to occur on a national scale? Who would enforce cybersecurity measures and provide guidance to businesses on what to do and how to react?
Though some federal guidance is still being worked out, the following is a roundup of five agencies that have a role in ensuring cybersecurity and responding to cyber incidents:
The Federal Bureau of Investigation:
Until recently, the level to which the federal government could get involved in a major private sector cybersecurity incident was unclear. But last month, the White House issued a presidential policy directive on cyber incident coordination. The PPD outlines the federal role and pledges that, in the case of a major private sector cybersecurity event, federal government responders will safeguard sensitive private sector information and abstain from interfering while remaining informed of the affected organizations response.
The PPD also directs that, in the event of a cybersecurity incident or threat, the FBI and the National Cyber Investigative Joint Task Force will take the response lead.
A relevant sector-specific agency will also work with the federal government to help it understand potential business or operational impact of a cyber incident on private sector critical infrastructure.
U.S. Secret Service:
Read Also: Nationwide Government Money Market Inv A
How Can I Help Cyber Police
You can make a complaint anytime to the cyber police or crime investigation department either offline or online. In order to give punishment for cyber crime, the first & foremost step is to lodge complaints against the crime. You need to file a written complaint with the cyber crime cell of any jurisdiction.
Cyber Security Tips For Small Business
Broadband and information technology are powerful factors in small businesses reaching new markets and increasing productivity and efficiency. However, businesses need a cybersecurity strategy to protect their own business, their customers, and their data from growing cybersecurity threats.
1. Train employees in security principles
Establish basic security practices and policies for employees, such as requiring strong passwords, and establish appropriate Internet use guidelines that detail penalties for violating company cybersecurity policies. Establish rules of behavior describing how to handle and protect customer information and other vital data.
2. Protect information, computers, and networks from cyber attacks
Keep clean machines: having the latest security software, web browser, and operating system are the best defenses against viruses, malware, and other online threats. Set antivirus software to run a scan after each update. Install other key software updates as soon as they are available.
3. Provide firewall security for your Internet connection
A firewall is a set of related programs that prevent outsiders from accessing data on a private network. Make sure the operating system’s firewall is enabled or install free firewall software available online. If employees work from home, ensure that their home system are protected by a firewall.
4. Create a mobile device action plan
5. Make backup copies of important business data and information
Recommended Reading: Do Illegal Immigrants Get Government Help
Other Ways Government Is Improving Cybersecurity
After high profile cyber hacking incidents, President Biden issued anExecutive Order on Improving the Nations Cybersecurity in May of 2021. Its main objectives are as follows:
- To improve tech security at the federal level by making IT systems stronger
- To improve the cybersecurity of federal contractors
- To establish baseline security standards for the development of software sold to the government.
- To require information technology companies to disclose cyber security issues and remove legal barriers to communicating with government entities.
With this Executive Order, the government hopes to make it more difficult to hack into government and government contractor systems. It also requires IT providers to disclose any cyber security breaches and makes it easier for them to work with the government.
Cybersecurity Employment In The Federal Government
The US federal government either does not know, or will not disclose, just how many of its employees work in cybersecurity. The number is surely in the tens, if not hundreds of thousands, however. The federal government is likely the worlds largest employer of cybersecurity personnel.
Each federal agency has its own internal security team. Agencies like CISA, the National Security Agency and the FBI have dedicated cybersecurity personnel. Many of the jobs require security clearances. Each branch of the military has its own substantial cyber operationsspanning intelligence, offensive and defensive cyber war. With the recent push for increased cybersecurity action and regulation, its a good time to be preparing for a career in cybersecurity with the federal government.
Don’t Miss: Government Help With New Windows
Us Department Of Homeland Security
- Under the National Protection and Programs Directorate , DHS leads the national effort to protect and enhance our cyber infrastructure. The National Cybersecurity and Communications Integration Center , overseen by NPPDs Office of Cybersecurity and Communications , is a cyber-situational awareness, incident response and management center for the Federal Government, the intelligence community and law enforcement. NCCIC handles incidents that may impact critical infrastructure and require technical response and mitigation assistance.
- In addition, the United States Secret Service has formed a network of Electronic Crimes Task Forces that focus on prevention, detection, mitigation and aggressive investigation of attacks on the nations financial and critical infrastructures. The USSS oversees cybercrime including computer intrusions or attacks, transmission of malicious code, password trafficking, or theft of payment card or other financial payment information.
- The Cyber Crimes Center is comprised of the Cyber Crimes Unit, the Child Exploitation Investigations Unit, and the Computer Forensics Unit under the Immigration and Customs Enforcement Homeland Security Investigations . C3 offers support to federal, state, local and international law enforcement agencies. ICE-HSI oversees cyber-based domestic or international cross-border crime including child exploitation, money laundering, smuggling and violations of intellectual property rights.
The Us Government Failed Their Cybersecurity Audit Now What

Cybersecurity News
From NASA to the State Department, federal agencies are relying on outdated systems, ignoring mandatory security patches and failing to protect classified data. On August 3rd, the Senate Homeland Security Committee released a bipartisan 47-page review of the federal government’s cybersecurity preparedness, and the title says it all: America’s Data Still At Risk. This was a follow-up to their 2019 report, America’s Data At Risk, which brought national attention to the shocking gaps that persisted across all branches of the US government. Two years and countless data breaches later, not much has changed.While the entire report is worth a read, here are some of the main concerns highlighted by the senators.
Read Also: Federal Government Benefits For Seniors
