Set Up Github Code Owners
Use the “code owners” feature on GitHub to hold contributing developers accountable for new changes introduced to open source projects. With this feature in a GitHub repository, developers can designate specific users as reviewers for changes introduced to certain parts of their codebase. Reviewers receive a notification when a pull request opens to the corresponding parts of the repository assigned to them.
This feature, paired with branch protections, ensures developers can review all pull requests before they merge into the main branch. This combination produces a greater level of quality assurance, because the contributors who are most familiar with the modified files verify the changes.
Next Steps
Real Solutions For Real Problems
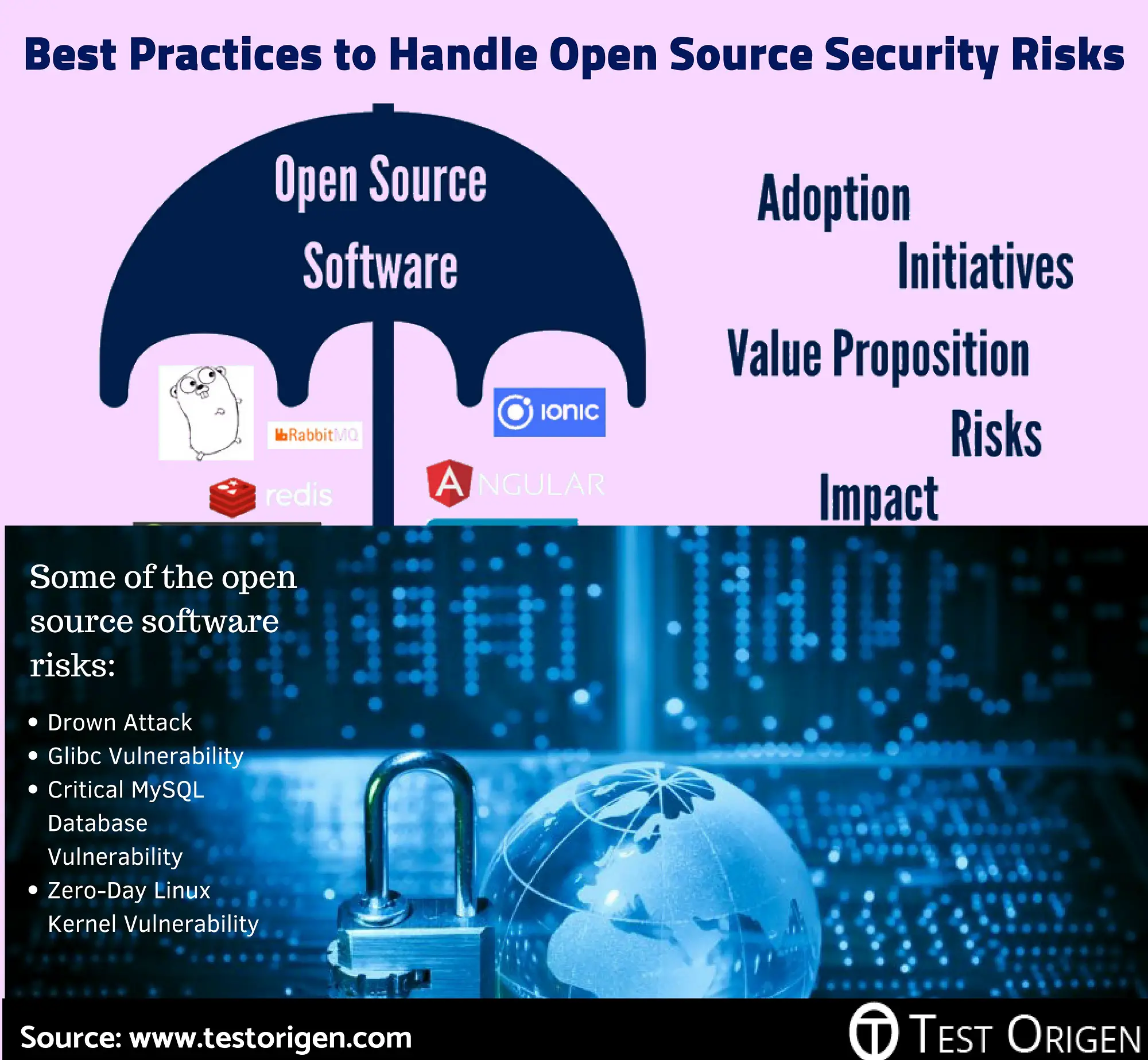
Open source code carries with it the potential for security, legal, and operational risks. If not handled properly, these risks can result in delayed release dates, extended go-to-market timelines, hundreds of thousands of dollars in remediation efforts, not to mention faulty usability and an unwanted customer experience for your end uses.
So whats a CTO to do? The answer is two-fold. Primarily, avoid affected components from entering your code. Secondly, know about vulnerable components and treat them before hackers exploit. The answer is, in other words, formulate a governance policy for your organization and execute it.
It is that the solution stage that a governance policy will get into the nitty gritty of choosing automation tools. Software composition analysis tools come in all shapes and sizes and their functionalities vary from one product to the next. These tools range in ability from detecting vulnerable components in the pre-pull stage and blocking vulnerable components from getting selected by developers, to detecting vulnerable components already in your code and pinpointing their location. SCA tools can be set to fit the security measures decided upon in your governance policy, so that they block vulnerable components of a certain severity but not another.
Datahub Data Governance Features
DataHub allows you to have fine-grained access control of the metadata. The access is driven by policies, which you can declare both from the web UI and the GraphQL API. DataHubs policies work on two layersplatform and metadata. Platform policies allow you to control user permissions for DataHub, for example, what features can a user see and use and to what extent. You can apply these policies to individual users or groups. On the other hand, metadata policies allow you to control what users can access different metadata entities and what operations they can perform on them. However, currently, DataHub doesnt let you control read permissions.
Data governance tools: LinkedIn DataHub. Source:
Several other features are part of the DataHub roadmap but dont have a clearly defined timeline as of now. One of the main data governance features is RBAC for entities and aspects . RBAC will not only enable finer access control for the metadata, but it will also help achieve better tag management, data preview access control, and so on.
In terms of governance/privacy: DataHub supports dataset-level classification, governed data movement, automated data deletion, data export, etc. They have plans to open-source some of the compliance capabilities, listed as part of their roadmap.
You May Like: How To Start A Data Governance Program
Who Is The Report For
This report is for everyone whose work touches open source software. Whether youre a user of open source, an OSS developer, or part of an OSS-related institution or foundation, you can benefit from a better understanding of the state of security in the ecosystem.
Open source consumers and users: Its very likely that you rely on open source software as dependencies if you develop software. And if you do, one important consideration is the security of the software supply chain. Security incidents such as log4shell have shown how open source supply chain security touches nearly every industry. Even industries and organizations that have traditionally not focused on open source software now realize the importance of ensuring their OSS dependencies are secure. Understanding the state of OSS security can help you to manage your dependencies intelligently, choose them wisely, and keep them up to date.
Open source developers and maintainers: People and organizations that develop or maintain open source software need to ensure they use best practices and policies for security. For example, it can be valuable for large organizations to have open source security policies. Moreover, many OSS developers also use other open source software as dependencies, making understanding the OSS security landscape even more valuable. Developers have a unique role to play in leading the creation of high-quality code and the respective governance frameworks and best practices around it.
Ways To Secure Open Source In Enterprises

May | 2020
Open Source has been a part of the corporate IT landscape for years. Organizations have benefited from using open source in many ways – right from reducing total cost of ownership, enabling better innovation, faster development, and better code quality, to attracting great talent to work for you.
However, one thing that is often seen as a possible issue with open source is security. One of the common arguments heard, for example, is that if anybody can contribute code to an open source project, what is stopping bad guys from inserting malware inside the projects you will use in your enterprise? And if you are using open source security products, can seeing the source code enable attackers to break the software and as a result your information system? Also, how do you ensure that the code you are using isnt riddled with known, yet unpatched, security vulnerabilities?
This article focuses on this need for security and discusses how to secure open source usage in enterprises by developing an adequate and healthy open source risk and security governance system.
Securing open source software usage
For security to succeed, it must become the default state for all processes, products and services used, developed, or offered by an organization. Accordingly, open source security has to be made mature and sustainable for it to be a positive asset.
There are several steps in securing the use of open source:
A holistic approach to open source security governance
You May Like: Government Jobs In Lakeland Fl
Addressing Cybersecurity Challenges In Open Source Software: What You Need To Know
The Linux Foundation | 01 September 2022
June 2022 saw the publication of Addressing Cybersecurity Challenges in Open Source Software, a joint research initiative launched by the Open Source Security Foundation in collaboration with Linux Foundation Research and Snyk. The research dives into security concerns in the open source ecosystem. If you havent read it, this article will give you the reports who, what, and why, summarizing its key takeaways so that it can be relevant to you or your organization.
Things To Know About Open Source
- 1
Open source is now a reality for all development teams.
- 2
Agile and DevOps have changed the equation. Itâs nearly impossible to build software entirely from scratch and still meet delivery deadlines.
- 3
Building software entirely from scratch also leads to higher development costs.
- 4
Open source offers essential and sometimes leading-edge software capabilities that canât be otherwise achieved.
- 5
Open source also carries potential risks, making a strong security policy the center of effective development today.
annual report
For more information about trends in software risks and vulnerabilities, review the latest version of our annual report, State of Software Security.
Recommended Reading: Top Government Contracts Law Firms
Contributions From Companies And Governance Models
Open source software is used by many different users. Because different companies will have their own need for the software, their contributions may change the scope. Companies may also have paid developers who are designated to join as project contributors to some projects.
These contributions should be treated as any other contribution. Governance continues to be based on the value of contributions and involvement.
snyk report
Is Open Source A Security Risk
Its no secret… developers use open source software.Still, there are questions around how it should be managed and for good reason.
Heres why:
- Open source components are not created equal. Some are vulnerable from the start, while others go bad over time.
- Usage has become more complex. With tens of billions of downloads, its increasingly difficult to manage libraries and direct dependencies.
- Transitive dependencies: if you are using dependency management tools like Maven , Bower , Bundler , etc., then you are automatically pulling in third party dependencies a liability that you cant afford.
Also Check: Report Misuse Of Government Funds
Openssf Announces 13 New Members Committed To Strengthening The Security Of The Open Source Software Supply Chain
Hosts Next OpenSSF Day in Dublin
SAN FRANCISCO, August 17, 2022 The Open Source Security Foundation a cross-industry organization hosted at the Linux Foundation that brings together the worlds most important software supply chain security initiatives, today announced 13 new members from leading financial services, technology, employment, software development, cybersecurity, telecommunications, and academic sectors.
New premier member, Capital One, joins the OpenSSF Governing Board. New general member commitments come from Akamai, Indeed, Kasten by Veeam, Scantist, SHE BASH, Socket Security, Sysdig, Timesys, and ZTE Corporation. New associate members include Eclipse Foundation, Purdue University, and TODO Group. We are excited to welcome new members to the OpenSSF, says Brian Behlendorf, General Manager of OpenSSF. As open source software security vulnerabilities continue to draw attention from governments and businesses around the world, interest in the work of the OpenSSF has been rapidly increasing.
A growing community of organizations, developers, researchers, and security professionals are investing the time and resources needed to strengthen open source security, said Jamie Thomas, OpenSSF Board Chair and IBM Enterprise Security Executive. New members of OpenSSF are joining at a time when cross-industry collaboration and innovation are needed more than ever to proactively respond to pervasive cybersecurity threats.
Premier Member Quote
The Move From Blind Eye To A Governance Policy
Historically the answer would have been a blind eye and deaf ear turned to open source usage and an undocumented, unmonitored free hand given to developers to choose open source components at their own discretion.
Fast forward down the production line and these unsuspecting developers begin to notice that the excessive freedom they enjoy spells out more trouble than benefit as they pull open source components without checking for vulnerabilities, without considering vulnerability severity, with little knowledge of the licenses attached to their components of choice, and find themselves a few weeks or months down the line in a world of remediation hurt.
In todays development climate, companies are questioning and negotiating the balance between getting their open source usage under control and managed in an automated, continuous and consistent manner, and leaving developers the freedom they need to productively do their jobs.
Recommended Reading: Government Assistance With Childcare Costs
When To Implement Governance
Governance should be implemented as soon as possible in any open source project. The earlier documentation is drawn up, the easier it is to define the expectations and goals. Early governance also allows roles to be clearly outlined. If the project is corporate or foundation backed, discussions should occur internally before launching the project so the processes are clear and there is a known path as the project moves forward.
Open Source Risk Evolves
Business and technology are undergoing unprecedented changes. The cloud, mobile technology, the Internet of Things , and fundamental advances in processing power have introduced opportunities to take your organization to greater heights. But, increasingly, gains are predicated on moving faster and faster. Open source code and software, while delivering speed and flexibility that align nicely with development models like DevOps, also shift whoâs responsible for coding quality and vulnerabilities that may lead to security gaps and breaches. But the challenges donât stop there. Numerous questions revolve around which specific libraries, components, and code an enterprise uses. Do these libraries contain vulnerabilities, and if so, what threat do they represent? Not all vulnerabilities are created equal, so itâs important to understand whether the vulnerability is actually dangerous and, if so, what level of damage it can cause. These challenges are exacerbated by the use of both direct and indirect open source libraries. In some cases, these indirect dependencies may extend five or 10 levels deep into a project or application.
Simply using open source libraries isnât a security threat to the business.
The real problem is not knowing that what youâre using contains vulnerabilities and that theyâre exploitable in your application.
GUIDE
Use our guide, Understanding Your Open Source Risk, to build a better open source security framework.
Don’t Miss: How To Order A Government Phone
Roles Within Open Source Governance
There are formal roles project contributors hold within open source software governance. Among the most recognized are:
Maintainer: This could be someone who has written a lot of code for the open source project or it could be someone who has produced documentation about the project or even an evangelist for the project. This contributor feels a sense of responsibility for the overall direction of the project and does whats necessary to make it better.
Contributor: Anyone who contributes to the project, whether it is commenting on problems or writing code. If they bring in something of value to the project, they play the role of contributor.
Committer: Someone with special commit access who has demonstrated deep and continuing commitment to the project.
What Is Open Source Governance
Open source governance is the recognized rules and customs that guide an open source project. According to OpenSource.com, in order to outline governance directives, the following questions need to be answered:
- What roles can contributors play in the project?
- What qualifications, duties, privileges, and authority are associated with each role?
- How do people get assigned to roles?
- How can role definitions be changed?
- What are the projects collective policies and procedures?
As the roles within the project are defined, usually based on each developers activities, governance of open source projects can be applied.
You May Like: Get Free Phone From Government
Apache Atlas Data Governance Features
Apache Atlas is especially good with classification. It can dynamically create data sensitivity, expiry, and quality classifications. This brings us to data lineage, another one of the sought-after features of Apache Atlas. Atlas implemented true data lineage, i.e., the lineage was actionable. Using the lineage data, Apache Atlas can propagate metadata properties to entities down the lineage hierarchy. This is one feature that you dont find as well-implemented in other data governance tools
Data governance tools: Apache Atlas. Source:
Apache Atlas has a range of data privacy and security features too. It has fine-grained access controls for entities and classifications. Atlas also works well with Apache Ranger to implement data authorization and masking. When working in tandem, these features form an effective data privacy and security safety net that allows the data to be masked or classified as PII, SENSITIVE, etc. It also gives you the framework to control who can access the PII and SENSITIVE data.
When And Where To Scan
A secure software development framework identifies and records all open source software components in use, as conducted through the process of Software Composition Analysis . Theres no single, ideal time in the development process to scan your codebase. Instead, it needs to happen continuously. Starting as early as possible in the processan expand-left approachcan address security and compliance issues before they grow more complex and more costly to remediate. .
Continuing right up until youre ready to release a product is equally important to ensure that your SBOM is complete and accurate. Given the complexity of todays products, not everything can be 100% automated. The human element still matters, as do common sense reviews. After all, automations are only as good as the policies that you create.
Where should this continuous scanning activity take place? Evaluate each of the following.
Scanning throughout a build will do a good job of identifying changes, but conducting periodic system-level deep dives is necessary, too. These are opportunities to look at the entire product, including its dependencies, the code youve written, and the third-party code thats been pulled in. A deep dive is the last gate to ensure that your product is secure when its ready to go out the door.
Also Check: Best Free Government Cell Phone Companies
Best Practices For Open Source Governance
Companies of all sizes and across all industries are creating software products and relying on open source code to do it. Both Forrester and Gartner, the industrys leading research and advisory firms, claim that anywhere between 80%-90% of all commercial software developers use open source components within their applications. But how is open source usage accounted for? How is it managed? Or is it?
Reducing Enterprise Application Security Risks:
More Work Needs to Be Done
Best Open Source Security Tools
Over the past quarter of a century, the open source movement has gone from strength to strength. But that success and the openness inherent in the community have led to a major challenge security. The more software that is developed, the greater the likelihood there is for vulnerabilities.
To make matters worse, the open source world prides itself on openness and transparency. Therefore, any security vulnerabilities are disclosed publicly. In this age of organized gangs of cybercriminals, that is like placing an ad asking for an attack.
This has given rise to a large number of open source security tools. They take care of all aspects of the management of security in open source components, examine dependencies, fix bugs in code, and lower risk.
However, the tools themselves vary considerably in scope, sophistication, and function. The editors of eSecurity Planet find the following 20 open source security tools to be particularly useful. Some are open source, some are commercial, but all are good security options for open source environments.
If youre interested in learning more about Open Source Security check out this book!
Read Also: Government Grants To Help Small Business
