Governance Risk Management And Compliance
Governance, risk management and compliance is the term covering an organization’s approach across these three practices: governance, risk management, and compliance. The first scholarly research on GRC was published in 2007 where GRC was formally defined as “the integrated collection of capabilities that enable an organization to reliably achieve objectives, address uncertainty and act with integrity.” The research referred to common “keep the company on track” activities conducted in departments such as internal audit, compliance, risk, legal, finance, IT, HR as well as the lines of business, executive suite and the board itself.
Governance Risk And Compliance Services
Deloittes governance, risk and compliance services help clients tackle the broad issues of corporate governance, enterprise risk management, and effective corporate compliance, while offering specialized assistance in key areas such as financial reporting, tax, information technology, human capital, anti-fraud and dispute consulting, and financial advisory services. We can help organizations identify, remediate, monitor, exploit and manage enterprise risks in addition to coordinating the utilization of people, process and technology to improve GRC effectiveness and help manage costs.
Explore Content
Leaders should consider embedding a thoughtful awareness of risk and compliance into the very fabric of the organization. People, processes and technology should all work together to help the enterprise stay in control of the risks it chooses to take.
Whether you need help and guidance at the board, C-level, or enterprise risk and compliance level, our professionals have deep experience in every major industry, so we can provide guidance and insight that makes sense for your unique business. Our services encompass:
Governance and oversight
- Improve board effectiveness
- Set the right tone and make effective decisions
- Assess and implement ethics programs, training, change management, anti-fraud programs and monitoring/reporting
Enterprise Risk Management
Corporate Compliance & Regulatory
Leaders Vs Laggards: The Three Greatest Ways They Differ
According to our survey, there are enormous differences in the ways companies that have suffered the lowest rate of loss in emerging economies and companies that have experienced the highest approach risk mitigation in the three major categories. From these differences, we have derived three rules that leaders follow to best mitigate overseas risk.
Read Also: Government Jobs Las Vegas Nevada
Governance Risk And Compliance Technology
Revolutionise your GRC conversations and accelerate the digital transformation of your internal audit, risk management and compliance functions.
Companies are facing unprecedented business and regulatory disruption. Its challenging the way organisations deliver GRC activities and has introduced new pressures on the digital infrastructure supporting them. Now, more than ever, our clients are seeking better models to digitise their functions, reduce costs and add value to the business.
Quantifying Risk: The Numbers
According to our survey, 83% of multinational companies have suffered significant losses in emerging markets since 2010, with an average cost per company over that time of $1.38 billion, and the average loss per year $260 million, or 0.7% of revenues.
In virtually all loss-making incidents , our respondents reported that the issue was either a matter of a regulatory violation, bribery or fraud, or reputational damage. In incidents with the highest losses, two or three of these types of risk converged: 60% of reported incidents involved more than one type, 35% involved two, and 25% were perfect storms that involved all three.
Regulatory issues are the most frequent cause of loss , but legal and criminal issues lead to the most expensive incidents. The most frequently cited consequences of getting caught were noted as reputational harm , loss of revenues , and prosecution . In all cases, reputational issues invariably make matters worse.
These are serious issues, and some companies respond with equal seriousness. Some do not.
Read Also: Congress Mortgage Stimulus Program Middle Class
About Managing Risk In Information Systems
Managing risk in IT is the process by which companies navigate potential uncertainty and damages using software and tools specifically designed to help do so. IT GRC tools may help determine and mitigate risks associated with the use, ownership, operation, involvement, influence, and adoption of IT within a company and for all the users involved.
Risk governance in IT is generally considered to be one part of a larger, all-encompassing risk management strategy for the enterprise. IT risk management may involve being able to define digital assets, having the ability to apply and monitor controls over IT systems, determine risks based on business criticality or technical severity, imagine and evaluate various remediation options, and set risk thresholds for IT processes.
Information technology is constantly changingevolving in scope, capabilities, and the laws that surround it. In that sense, compliance control is vital to ensure your processes are always up-to-date, particularly around security and privacy protocols.
Governance Risk & Compliance Tool Comparison
There are a range of factors to consider when comparing GRC tools:
Business-wide GRC vs. system-specific: GRC tools vary in their scope of governance and compliance capabilities. Some products offer an all-in-one experience for governing data and facilitating regulatory compliance across the entire business. However, others focus on specific environments or processes, such as Office 365 systems or data integration processes. Buyer should consider what specific areas or processes require GRC support, and what scope best fits their needs.
Compliance focused vs. process-focused: Governance, risk management, and compliance tools usually focus on two business goals- preventing losses of data or resources, and ensuring regulatory compliance. Most GRC tools can serve both goals, but they may be more specialized in one area over the other. For instance, resource control-focused GRC platforms will emphasis Data Loss Prevention or policy management, while compliance-focused tools will prioritize reporting and audit support.
Don’t Miss: Los Lunas Gov
Tips When Implementing Grc
Implementing a GRC model can seem complex, as it will generally include internal auditing of existing processes and procedures. Its likely that each established area of the organization will have its own way of performing risk assessments or compliance monitoring. But a unified approach with shared expertise is the best way to achieve the overall aims of the organization.
With this in mind, there are ways to make the launching of the GRC program more straightforward. Here are five tips for implementing a GRC framework in an organization.
Grc Software And Tools
GRC software combines applications that manage the core functions of GRC into a single integrated package. It enables an organization to pursue a systematic, organized approach to managing GRC-related strategy and implementation. Instead of using siloed applications, administrators can use a single framework to monitor and enforce rules and procedures. Successful installations enable organizations to manage risk, reduce costs incurred by multiple installations and minimize complexity for managers.
Effective GRC software includes risk examination and risk assessment tools that identify linkages to business processes, internal controls and operations. GRC software will identify the processes and tools that control those risks and integrate the single, multipoint and enterprise-wide software the business currently uses.
GRC software also provides a structured approach for compliance with legal and regulatory requirements, such as those specified in the Sarbanes-Oxley Act, General Data Protection Regulation, or occupational health and safety regulations.
Other features offered in GRC platforms include operational risk management information technology risk management policy audit management third-party risk management issue tracking and document management.
GRC software considerations
GRC software products are available from a number of vendors. Products accommodate virtually any type or size of organization, including organizations with many lines of business.
Read Also: Access Wireless Replacement Phone
What Is Integrated Risk Management
Integrated risk management goes hand in hand with governance, risk, and compliance.
Gartner defines integrated risk management as follows:
Integrated risk management is a set of practices and processes supported by a risk-aware culture and enabling technologies, that improves decision making and performance through an integrated view of how well an organization manages its unique set of risks.
Some of the many attributes of integrated risk management include:
- Strategy
- Communication and reporting
- Monitoring
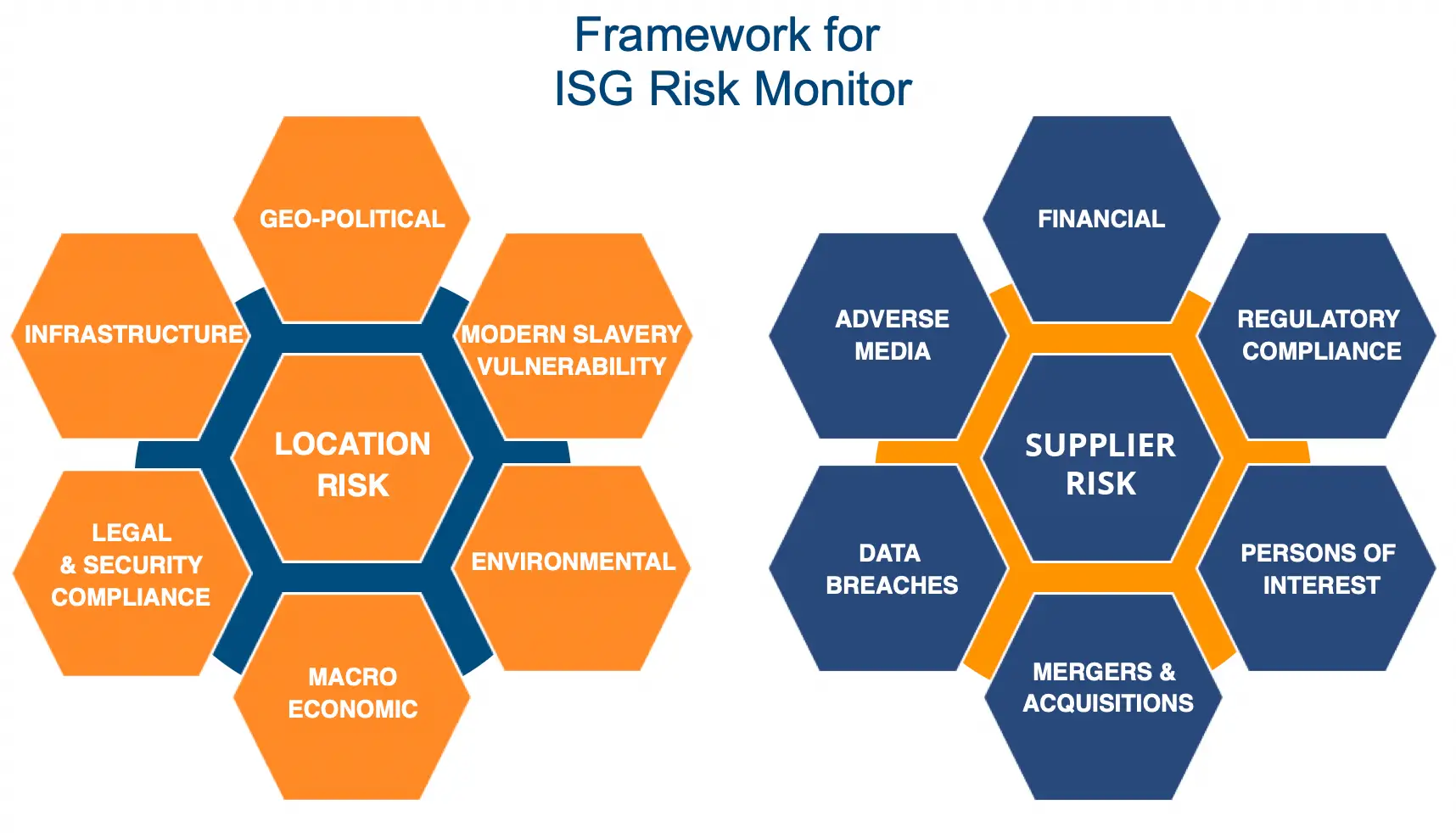
To understand the many risks associated with your organization, you need a comprehensive overview of all risk and compliance functions, along with any external connections, such as suppliers and business partners.
With the help of a GRC platform, you gain access to the tools you need to assist with IRM.
What Is Grc Software
Governance risk management and compliance software is a means for publicly-held enterprises to manage IT-related operations that require regulation and ensure they are meeting compliance and risk standards. Risk navigation software tends to center around four components: strategy, processes, technology, and people. With this type of software solution, its easier and more efficient to:
- Conduct an internal audit
- Gain control over your incident management plan
- Implement automation to save your organization time and money
- Focus on policy management
- Streamline internal communication
Now that you understand the basics of GRC software, Ill turn my attention to why implementing a compliance platform is a good idea.
Don’t Miss: City Of Las Vegas Government Jobs
Why Does Your Organization Need Grc
Organizations face a rapidly changing and increasingly complex business climate. Whether youre part of a large corporation, government agency, small business or nonprofit, youll face numerous challenges, including:
- Constant changes to regulations and enforcement that severely impact business operations
- Stakeholder demand for strong performance outcomes, consistent growth and transparent processes
- Growing costs of addressing compliance requirements and managing risk
- Increase of third-party relationships and associated governance challenges
- Potential legal and financial consequences resulting from lack of effective oversight and overlooking critical threats
A disorganized approach to GRC can slow down an organization and cost more all while achieving less, missing requisite compliance requirements and misidentifying threats to your revenue or reputation.
The Three Pillars Of Grc

Governance: It is the mechanism by which top management can direct and influence the organization across all levels. Governance involves orchestrating rules, policies, processes, and controls that ensure the alignment of corporate objectives with the organizations business goals.
Risk Management: Risk is any event that has the potential to cause loss or harm to the organization. In the context of GRC, risk management requires the identification, assessment, and control of legal, strategic, financial, and security risk to an organization.
Compliance: The goal of compliance in GRC is to ensure that the organization adheres to a standard or set of rules, industry guidelines, policies, and regional laws that are mandated by the respective industries and/or government agencies. For IT, this translates to protection of data and ensuring authorized access to data.
Also Check: City Jobs In Las Vegas Nv
Why Companies Large And Small Need Grc
- Stakeholders demand a high degree of transparency, accountability, and performance.
- Regulations are constantly changing in an unpredictable manner.
- Third party relationships and risks are growing exponentially, which is a challenge to management.
- The lack of risk identification has harsh impacts.
- Efficiency gains through GRC are necessary for business growth.
Clear Lines Of Responsibility
Designate the parties responsible for specific functions in Azure
Clearly documenting and sharing the contacts responsible for each of these functions will create consistency and facilitate communication. Based on our experience with many cloud adoption projects, this will avoid confusion that can lead to human and automation errors that create security risk.
Designate groups that will be responsible for these key functions:
| Group or individual role | |
|---|---|
| Typically IT operations, security, or jointly. Monitor and remediate server security . | |
| Incident Monitoring and Response | Typically security operations team. Investigate and remediate security incidents in Security Information and Event Management or source console. |
| Policy Management | Typically GRC team + Architecture. Set Direction for use of Role Based Access Control , Microsoft Defender for Cloud, Administrator protection strategy, and Azure Policy to govern Azure resources. |
| Identity Security and Standards | Typically Security Team + Identity Team jointly. Set direction for Azure AD directories, PIM/PAM usage, MFA, password/synchronization configuration, Application Identity Standards. |
You May Like: Governmentjobs Com Las Vegas
The Discovery Phase Is Important
Spending time taking stock of existing processes is vital if the GRC program is to be a success. Organizations should perform an internal audit of the processes and procedures used by the risk assessment and compliance teams.
Approaches in departments and teams fields will of course be different, but the aim is to establish the similarities and shared processes. The results of the internal audit will help shape the direction of the whole GRC project.
Its also important to define all relevant regulations, contracts, laws and legislation the organization may need to be compliant with. For example, organizations that process cardholder data will likely need to be compliant with the Payment Card Industry Data Security Standard. Once highlighted, the scale and scope of the GRC program can be decided.
Solarwinds Security Event Manager
SolarWinds Security Event Manager is an on-premises software package that performs log management and security scanning. It is a suitable system for ensuring compliance to PCI DSS, GLBA, SOX, NERC CIP, and HIPAA, among other standards.
The Security Event Manager works as a log collector and consolidator to create. The log files that the system compiles then feed through to a SIEM system for intrusion detection. Those logs dont get discarded they contribute to ongoing system activity tracking and they are also available for compliance auditing. All log files are protected from tampering.
The risk assessment requirements of GRC are covered by vulnerability scans that identify weaknesses, such as out-of-date software. The SIEM system also has a built-in remediation mechanism. The service gives you options over which events should raise alerts for manual analysis and which should trigger automated responses. The SIEM is able to communicate with Active Directory to suspend suspicious user accounts or with firewalls to blacklist IP addresses. All actions taken by the Security Event Manager are logged.
Compliance risk reporting and standards goal auditing can all be tailored within the system towards specific standards requirements. Status and event reports can also have graphical content to improve conformance proof.
The Security Event Manager installs on Windows Server and it is available for a 30-day free trial.
EDITORS CHOICE
Operating system: Windows Server
Recommended Reading: What Is The Best Free Government Cell Phone
Project Management Institute Risk Management Professional
Anyone who has pursued a project management certification is familiar with the Project Management Institute , either through research or by picking up the coveted Project Management Professional credential. However, PMI also offers the Risk Management Professional certification, as well as several others that focus on business management, business analysis, agile and scheduling.
The PMI-RMP identifies IT professionals involved with large projects or working in complex environments who assess and identify project-based risks. They are also competent in designing and implementing mitigation plans that counter the risks from system vulnerabilities, natural disasters and the like.
The PMI-RMP exam covers five knowledge domains: Risk Strategy and Planning , Stakeholder Engagement , Risk Process Facilitation , Risk Monitoring and Reporting and Perform Specialized Risk Analyses . The exam has 170 multiple-choice questions, takes up to 3.5 hours to complete and costs $520 or $670 .
You must also meet experience and education requirements. One option is to have a secondary degree , and at least 4,500 hours of project risk management experience and 40 hours of project risk management education. The second option is a four-year degree , at least 3,000 hours of project risk management experience and 30 hours of project risk management education.
A Grc Framework That Shifts Overhead Cost To Value Driver
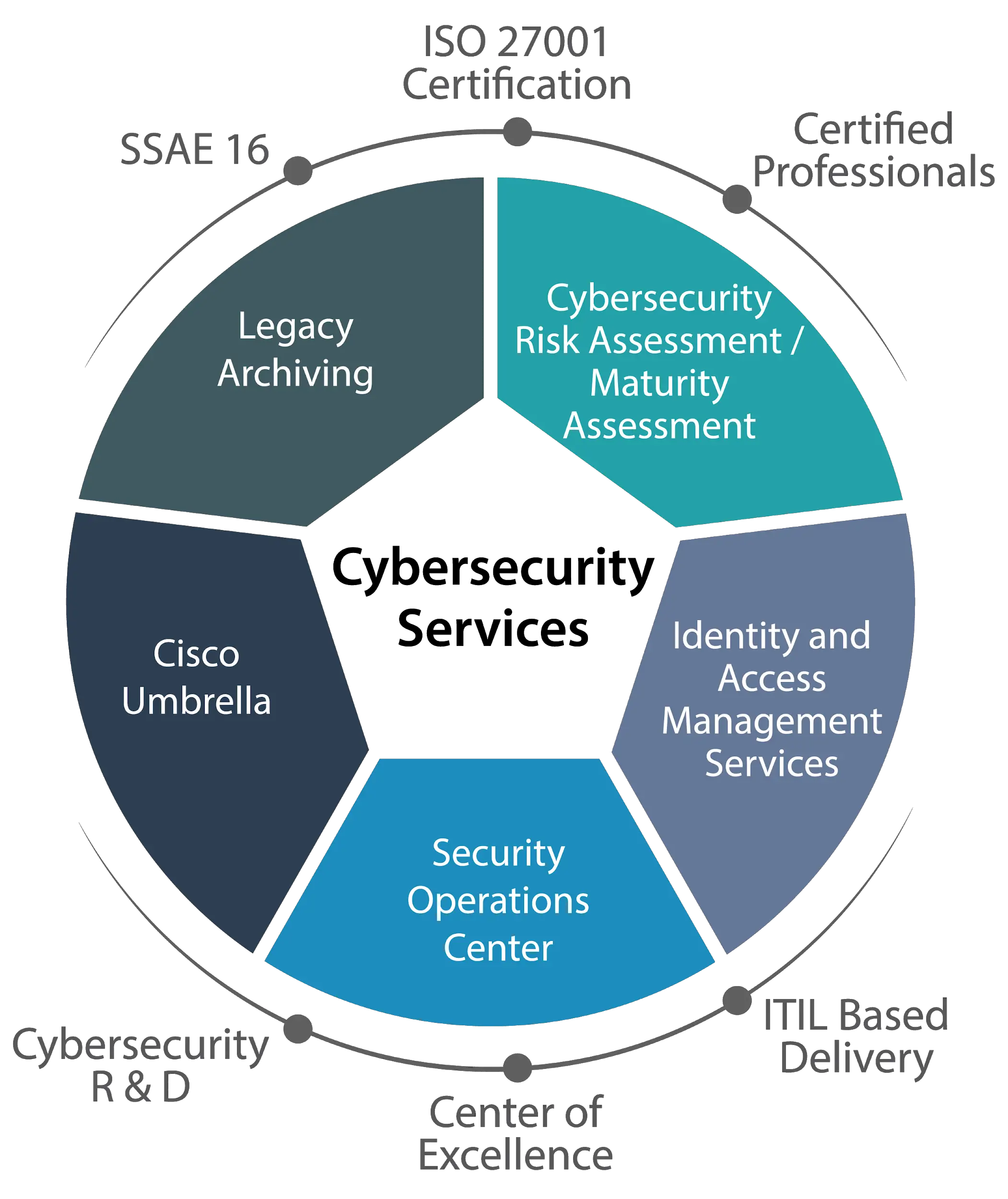
Our GRC solutions combine real-time monitoring, reporting, and analysis to help companies comply with regulations and prepare for unexpected events. GRC focuses on five key services to address specific, high-profile business challenges around risk governance and GRC security. These services are:
- Concurrent Audit
- Regulatory Compliance
Also Check: Government Grants For Dental Implants
Assign Incident Notification Contact
Ensure a security contact receives Azure incident notifications from Microsoft typically a notification that your resource is compromised and/or attacking another customer.
This enables your security operations team to rapidly respond to potential security risks and remediate them.
Ensure administrator contact information in the Azure enrollment portal includes contact information that will notify security operations
What Is Grc Used For
GRC provides a structured approach to achieve governance, manage organizational risk and ensure compliance with regulations. GRC helps organizations align their IT with business objectives while effectively establishing best practices, managing IT and financial risks, improving decision-making, controlling costs, reducing silos, and acting with integrity.
Also Check: Grb Platform
What Is An Integrated Approach To Risk Management
Effective GRC must:
- Be driven by industry leaders like CISOs, CROs, CIOs, CFOs, CEOs, legal, etc.
- Have a risk-focused culture.
- Be built on a modern, integrated, cloud-based platform.
- Integrate easily with other technologies in the ecosystem to collect data.
- Make data sharing easy to be able to cross leverage common data.
- Target and address business risk throughout the organization and third-party ecosystems
- Create business-oriented, process-based workflows to analyze and treat risk.
- Embed risk intelligence and workflows into daily/operational tools.
- Make risk and compliance available at everyones fingertips.
- Enable continuous monitoring of risks and controls through the use of automated risk indicators.
- Explain risk in business terms through business-focused dashboards
- Do it all on an on-going basis for departments and functional groups across the enterprise, and with vendors, to provide a holistic, real-time view of risk.
Regularly Review Critical Access
Regularly review roles that are assigned privileges with a business-critical impact.
Set up a recurring review pattern to ensure that accounts are removed from permissions as roles change.You can conduct the review manually or through an automated process by using tools such as Azure AD access reviews.
Recommended Reading: City Of Las Vegas Government Jobs
Permission Guidance And Tips
-
To drive consistency and ensure application to future subscriptions, permissions should be assigned at management group for the segment rather than the individual subscriptions. See Avoid Granular and Custom Permissions for more details.
-
You should first review the built-in roles to see if one is applicable before creating a custom role to grant the appropriate permissions to VMs and other objects. See Use Built in Roles for more details
-
Security managers group membership may be appropriate for smaller teams/organizations where security teams have extensive operational responsibilities.
