The Native Data Governance Controls In Snowflake
Modern organizations are increasingly relying on data analytics to guide business decisions. To quickly process data for analytics, organizations are utilizing applications like Snowflake. With its unique architecture, Snowflake can handle nearly unlimited concurrent workloads, helping organizations run complex queries quickly and securely.
However, with the massive amount of data running in Snowflake, organizations need to ensure robust data governance controls are implemented to ensure data integrity and security.
Snowflake has several data governance controls embedded in the application. For example:
- OAuth – a standard protocol that allows supported clients authorized access to Snowflake without sharing or storing user login credentials.
- Network policies – for limiting/controlling site access by user IP address. Admins can create IP allow and IP block lists.
- Object-level access control – granular control over access to objects who can access what objects, the operations that are allowed on those objects, and the roles that can create or alter access control policies.
- Row Access Policies – to enforce access policies that determine which rows are visible in a query result.
- Object Tagging – to apply tags to Snowflake objects. This tagging helps track sensitive data and resource usage.
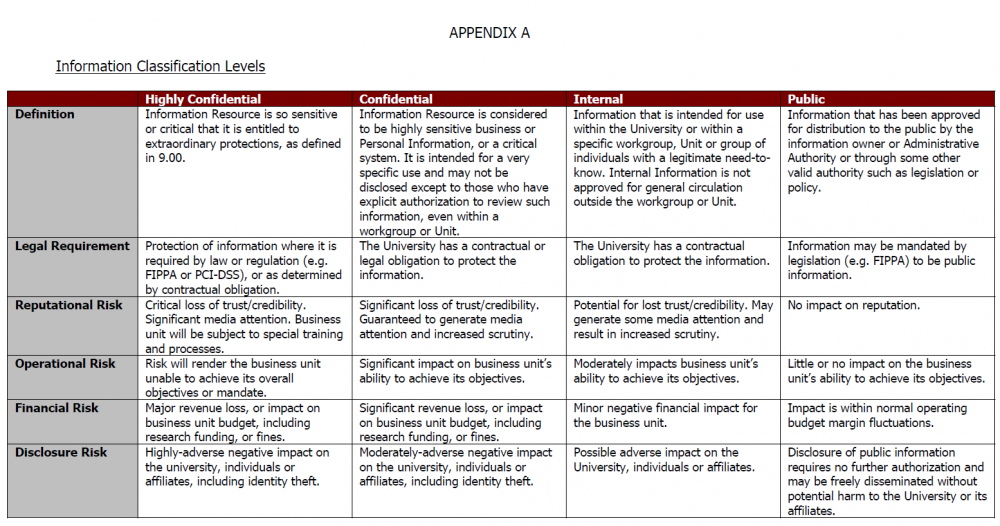
Example Of A Basic Classification Scheme
The simplest scheme is three-level classification:
- Public data Data that can be freely disclosed to the public. Examples include your company contact information and browser cookie policy.
- Internal data Data that has low security requirements but is not meant for public disclosure, like marketing research.
- Restricted data Highly sensitive internal data. Disclosure could negatively affect operations and put the organization at financial or legal risk. Restricted data requires the highest level of security protection.
What Is Data Classification Guidelines And Process
Imagine youre the CISO of a 10,000-person organization where users create millions of files and emails each day. Some of that information is highly sensitiveif leaked or stolen, youre facing a headline-making breach and seven-figure penalties. Most of the data created each day, however, could be published on the front page of the Times without incident.
It can be virtually impossible to prioritize risk mitigation or comply with privacy laws when you dont know which information calls for military-grade protection. Thats where data classification comes in.
Recommended Reading: How To Get A Grant To Start A Trucking Business
Why You Need To Keep The Policy Up
The only thing more important than having a data classification policy is keeping your policy up-to-the-minute current. OK, up-to-the-minute is slightly exaggeratedbut with the expected expansion of privacy regulations in the future, it might not be far off.
Updating your data classification policy is critical in achieving your teams infosec management objectives. Every data-related decision made across the enterprise should be based on correct, updated data classification status. Successful companies stay abreast of both internal changes such as adoption of new technology systems and outside regulatory requirements, and update their data classification policies accordingly. Further, they make sure that all team members handling systems and data are fully aware of whats in the current version of their data classification policy.
Key Data Classification Terms And Definitions
Data classification is the process of organizing structured and unstructured data into defined categories that represent different types of data. Standard classifications used in data categorization include:
- Public
- Sensitive
- Personal
Sensitive data is a general term representing data restricted to use by specific people or groups. Sensitive and confidential data are often used interchangeably. Examples of sensitive data include intellectual property and trade secrets.
Data reclassification is re-categorization of data to apply appropriate updates, for example, based on changes to legal or contractual obligations, data usage or value, or new or revised regulatory mandates.
Data tagging or labeling adds metadata to files indicating the classification results.
Recommended Reading: Semper Fi Auto Repair Las Vegas
Examples Of Restricted Data
- Donor/prospect contact information and non-public gift information
- Audit reports
- Individually identifiable data on race, color, ethnicity, religion, sex, national origin, age, ancestry, disability, status as a veteran, sexual orientation, marital status, parental status, gender identity, gender expression and genetic information
- Competitive business information
- Faculty/staff employment applications, personnel files, benefits, birth date, personal contact information
- Location data for devices connected to KU wired and wireless networks
- Data subject to non-disclosure agreements
- Conflict of Interest disclosures
- Bulk email addresses
Internal – This data may be accessed by employees of the university for purposes of university business.
How Do You Handle Your Data Classification
Data classification, or information classification as it is sometimes known, is the process of classifying an organisations data to ensure it receives an adequate level of protection. Organisations will usually develop a data/information classification policy that determines which type of data falls within each level of classification and how that data should be protected. They then go about classifying their data with the levels of classification in their data/information classification policy.
How do they handle this process of data classification?Organisations use a multitude of methods to classify their data. Some methods are prone to human frailty, others are not so. One method that is quite common is stamps people will have a stamp for each level of classification confidential, public, etc and then just merely stamp each document that they handle. Sure, this is effective in some cases, and its a practical solution in environments where there is a lot of paperwork. However, it is prone to human failure documents can slip through without being classified and therefore dont receive the correct handling to protect the information they contain.
Another method for applying data classifications is by inserting a footer into electronic documents. This is also prone to human failure as there is no easy way to ensure a classification is applied to a document.
If you want to classify your information effectively, you need Boldon James Classifier!
Also Check: Free Dental Implants Grants
What Does Gdpr Request In Terms Of Data Classification
To comply with the GDPR, originations need to incorporate controls like data discovery, data profiling, taxonomies for data sensitivity, and data asset cataloging. To classify data, companies may need to consider the following:
- Type of data
- Basis for data protection
- The categories of the individuals involved
- The categories of recipients
Enforce The Classification Policy And Take Advantage Of The Benefits
The best way to ensure consistency in information handling across the entire organization is to deploy a classification tool that enforces users to classify information at the point of creation.
In this case, users are immediately prompted to input classification labels based on the set customized scheme for the business.
The customized classification parameters can be set by sensitivity, the level of confidentiality required for the data, and by domain, the department or user type with restricted access to different types of data.
Forcing users to classify every document, email, and download causes them to slow down and truly think about the nature of the information they handle and the sensitivity of what it contains.
This brings security risks to the forefront and increases awareness throughout the organization.
Also Check: Safelink Wireless Las Vegas
What Does Pci Dss Request In Terms Of Data Classification
Data classification is requested in terms of regular risk assessment and security categorization process. Cardholder data elements should be classified according to their type, storage permission and required level of protection in order to ensure that security controls apply to all sensitive data as well as confirm that all instances of cardholder data in the environment are documented and that no cardholder data exists outside of the defined card holder environment.
According to the Netwrix 2020 Data Risk and Security Report, 75% of financial organizations that classify data can detect data misuse in minutes, while those who dont mostly need days or months . This highlights the importance of data classification for PCI DSS compliance purposes.
75% of financial organizations that classify data can detect data misuse in minutes, while those who dont mostly need days or months
Source: 2020 Data Risk & Security Report
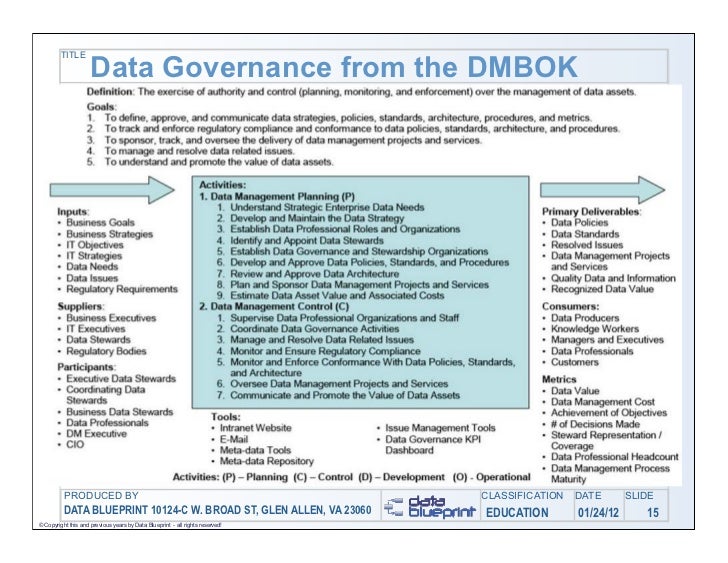
Roles In The Framework
Chief Data Officer
Chief Data Officers are a fast-growing job over the last few years. Companies are beginning to understand the importance of managing data and implementing a data governance framework, and that means hiring a CDO. The CDO is the company leader of the data governance strategy, and hiring a CDO shows the commitment to data and buy-in from the top to take a data governance program seriously.
Data Owners
Data Owners are the people that have direct responsibility for data. They are involved in the protection and quality of data as a business asset. A data owner will be on the team that uses the data. For example, a member of the finance team should be a Data Owner for the Finance teams data.
Varonis automates the process for Data Owners to manage access to their data. Data Owners know who in their organization should have access to their data, and providing them the tools they need to manage and audit access to data is good data governance.
Data Stewards
Data Stewards are the champions of your data governance strategy. They meet with Data Owners and enforce data governance policies and procedures, as well as train new data owners and employees in data governance.
Data Governance Committees
The Data Governance Committee sets policies and procedures for data governance. This committee works with the CDO to establish the who, what, when, where, and why of data governance.
Don’t Miss: Government Jobs In Sacramento
Types Of Data To Be Classified
Almost every organization houses some type of sensitive data often much more than they realize. Each must understand the specific types of sensitive data within their enterprises and execute data classification in ways that support optimized data privacy, security, and compliance.
Data that needs to be classified is often called sensitive data. This means that if it is exposed inside or outside of the organization it presents risks to individuals privacy and security, or that it risks falling out of compliance with leading data protection regulations.
A well-known study using U.S. Census data estimates that the identity of 87% of Americans can be determined using a combination of the persons gender, date of birth, and ZIP code. When taken separately, these details might not seem sensitive. However, a breach of those three elements would likely also compromise the individuals name, home address, Social Security number, and other personal data. As a result, those elements should be considered sensitive.
Overall, data housed within todays organizations can be categorized into two broad categories: regulated and unregulated data . General types of information fall under each main category.
Develop A Formalized Classification Policy
An organizations classification policy overviews the who, what, where, when, why, and how, so that everyone understands the role that data classification plays across the enterprise. Points to cover in the policy include:
Objectives Overview the reasons why data classification has been put into place and the goals the company expects to achieve.Workflows Explain how the classification process will be organized and how it will impact employees who use different categories of sensitive data.Schema Describe the data categories that will be used to classify the organizations data.Data owners Outline the roles and responsibilities of everyone involved in managing data classification, and how they classify sensitive data and grant access.
You May Like: Sacramento Federal Jobs
Developing A Data Governance Policy
Once those assessments are done, the data governance committee should use its determinations to develop the policy guidelines and procedures that, if followed, ensure the enterprise has the data program envisioned by the committee.
A well-crafted policy creates a governance framework that ensures the following:
- the appropriate level of oversight of the organization’s data assets based on their value and risk as determined by the data governance committee
- consistent, efficient and effective management of the data assets throughout the organization and over time and
- the appropriate protection and security levels for different categories of data as established by the governance team.
A well-articulated policy also helps ensure that the enterprise data governance structure supports the organization’s strategic vision for its data program, whether the goal is leveraging data to glean insights that drive new revenue or to use data to provide new services or to fuel digital transformation more broadly.
Many governance committees select one of the available data governance policy frameworks to identify the elements they need to address and determine the standards and guidelines that will work for their organization’s needs. Generally, as part of crafting and finalizing a data governance policy, data governance councils will also need to identify the roles responsible for managing and enforcing the guidelines laid out in the policy.
Data Security Events Or Weaknesses
Users of information systems or services must report any detected or suspected security events or weaknesses to the relevant Data Steward as soon as possible.
Where a data security event involves personal information, the user and/or Data Steward must notify the Universitys Privacy Officer on 9479 1839 or as soon as possible, or in any event 24 hours of discovery as per the Universitys Data Breach Response Plan.
Major data security events and/or breaches will be managed in accordance with the Universitys Critical Incident Management Policy.
Don’t Miss: Polk County Fl Forclosure
Data Classification For Hipaa
The HIPAA Security Rule establishes baseline administrative, physical and technical safeguards for ensuring the confidentiality, integrity and availability of electronic protected health information . PHI is similar to personally identifiable information, as discussed above. PHI is considered as any individually identifiable health information, including:
- Mental health history
- Payments for healthcare
- Other identifiable information, such as patients name, address or Social Security number
ePHI is defined as any protected health information that is stored in or transmitted by electronic media. Electronic storage media include computer hard drives, as well as removable or transportable digital memory media like optical disks and digital memory cards. Transmission media include the internet or private networks. Common examples of ePHI include:
- Name
- Address
- Any date directly related to an individual, including birthday, date of admission or discharge, or date of death, as well as the exact age of individuals older than 89
- Telephone or fax number
Keep The Snowflake Data Governance Process Flexible:
Like any process, Data governance takes multiple iterations to perfect. It is a continuous process with a strong focus on feedback-based improvements. As new data streams join in, data volumes grow, and new access points emerge, the Data governance process will be used to come up with new policies to address new challenges. Therefore, it is important to keep it adaptable.
Data governance teams also need a thorough review process that constantly assesses governance policy enforcement and effectiveness. The results of the review process will help formulate improvements.
Don’t Miss: Good Jobs For History Majors
What Is A Data Governance Policy
A data governance strategy is a set of guidelines, which ensure that data assets are consistently managed and correctly used. These guidelines typically include individual policies regarding data quality, access, security, privacy, as well as roles and responsibilities for implementing these policies and monitoring compliance.
A data governance strategy should clarify the principles, practices, and standards that the organization deems necessary to have high quality data and protect data assets. This process is the responsibility of a group called the Data Governance Committee, which consists primarily of executives and data owners.
Policy documents developed by this team should clearly define the data governance structure that executives, managers and production line workers must follow in their day-to-day routines.
Here are some important basic data policies that any organization should establish.
Learn more in our detailed guide to data governance policies
Why Do Organizations Need Data Governance
More and more, in-house information is finding a new life as a valued asset across the entire organization rather than simply as the property of individual departments. In fact, many data governance initiatives originate as attempts to improve data as it becomes actionable across the organization. Data is now used to develop organizational efficiencies, identify profit opportunities, enhance customer experiences, and improve or develop new products.
However, two of the primary reasons for data governance are regulatory mandates and risk assessments that rely on high-quality data. In particular, many regulations focus on an organizations data to show proof of compliance, especially in the area of data security. According to the 2013 Rand Secure Archive Data Governance Survey, 82 percent of respondents know they face external regulatory requirements, but 44 percent of those respondents still dont have a defined data governance policy.
Areas that benefit from data governance include those that require regulatory reporting data to meet guidelines for Sarbanes-Oxley Basel I, II, and III COBIT Dodd-Frank cGMP ISO/IEC 38500 and elements of the Health Insurance Portability and Accountability Act .
Recommended Reading: Engineering Management Gwu
Data Governance Policy Templates
Although policy templates are available to help organizations organize their approach to creating their own data governance policy, some advisers have cautioned against relying on them — or relying on them exclusively — because a strong, well-crafted policy should be unique to each organization, addressing:
- the organization’s vision for its data governance program
- the program’s structure, including roles and responsibilities
- data standards and guidelines, along with the procedures and programs to enforce them, to deliver on the organization’s data governance objectives and
- how adherence to the policy will be monitored, measured and remedied as well as when the policy should be reviewed and how it should be updated.
Next Steps
Implementing Your Data Classification Framework In Microsoft 365
Once you have developed your data classification framework, your next step is implementation. The Microsoft 365 compliance center allows administrators to discover, classify, review, and monitor their data in accordance with their data classification framework. Sensitivity labels can be used to help protect your data by enforcing various protections such as encryption and content marking. They can be applied to data manually by default, based on policy settings or automatically, as the result of a condition such as identified PII.
For smaller organizations or organizations with a relatively streamlined data classification framework, creating a single sensitivity label for each of your data classification levels may suffice. The following example shows a one-to-one data classification level to sensitivity label mapping:
| Classification label |
|---|
| All users |
During a Microsoft internal information protection pilot, there were difficulties with the understanding and use of the ‘Personal’ label. Users were confused as to whether this meant PII or merely related to a personal matter. The label was changed to ‘non-business’ to be clearer. This example shows that taxonomy does not need to be perfect from the start. Start with what you think is right, pilot it, and adjust the label based on feedback if needed
Recommended Reading: Polk Real Foreclosure