The Emerging Cybersecurity Maturity Model Certification Requirement
The Cybersecurity Maturity Model Certification is a new set of cybersecurity standards the DoD is implementing to ensure a higher rate of compliance. Before CMMC, Defense Industrial Base contractors were responsible for conducting their own security checks, but CMMC requires third-party assessments to ensure the requirements are being met.
With CMMC, contractors in the DIB must have the maturity of their network’s security evaluated on a five-tiered scale. It’s important to note you don’t necessarily have to meet all five tiers, defense contractors only need to meet tier 3 to fulfill their requirements since it closely aligns with the current DFARS 252.204-7012 requirements .
CMMC 1.0 was released in January of 2020 and audits are expected to begin in 2021, so it’s important you begin preparing now. Although this requirement mainly applies to defense contractors, other contract vehicles such as 8 STARS III are beginning to mandate CMMC, so it could soon become a qualification for all federal contractors.
Contractors should make sure they are compliant with DFARS 252.204-7012. To learn more about how you can meet the CMMC requirements, watch our webinar, “How to Succeed Under CMMC: Small Business Solution for Defense Contractors.”
How Cmmc Changes Nist 800
In light of evidence that a woefully small percentage of defense contractors were actually complying with NIST 800-171, the DoD began rolling its security requirements into the CMMC in 2019. The first major change is that self-assessment will no longer be enough: after October, contractors will be required to undergo third-party review to demonstrate their compliance with DFARs.
While that means that organizations will have to tighten up their compliance strategy, a second development will make the burden easier to bear: a single standard for compliance will no longer be applied to all defense partners. Under CMMC, there are five security levels and while all require NIST 800-171 to be followed in some degree that degree changes between levels:
After pending updates to the DFARs rule, compliance with NIST 800-171 will expand to second and third-party businesses and vendors working with a Defense contractor, and at level 3 and beyond the contractor will be required to ensure that their partners are compliant. Consequently, DFARs requirements will soon be extending to a much larger group of businesses than those working directly with the DoD.
What Does This All Mean
The new contract data requirements list carries significant implications, both for direct recipients of DoD contracts and for subcontractors of those direct recipients. By including this single requirement in section J of a solicitation or contract award, an acquisition officer will have full documentation of the following:
- All of your Tier 1 Level Suppliers who receive covered defense information . For most DoD prime contractors: this represents an unprecedented amount of insight into their supply chain.
- If you are a subcontractor: this may be the first time DoD knows who you are.
Read Also: Mortgage Stimulus Program Middle Class
Conduct A Security Assessment
Conduct a security assessment once you’ve implemented all NIST 800-171 controls. This assessment should closely examine all systems and processes for noncompliance issues. NIST 800-171 requires contractors to perform these assessments on a regular basis, typically quarterly or annually.
Regular assessments help ensure that the current processes continue to provide adequate protection of CUI. It’s especially important to conduct another assessment after implementing system changes. Periodic assessments also minimize the threat posed by new methods of attack by malicious actors.
Viii Paperwork Reduction Act
The Paperwork Reduction Act of 1995 provides that an agency generally cannot conduct or sponsor a collection of information, and no person is required to respond to nor be subject to a penalty for failure to comply with a collection of information, unless that collection has obtained OMB approval and displays a currently valid OMB Control Number.
DoD requested, and OMB authorized, emergency processing of the collection of information tied to this rule, as OMB Control Number 0750-0004, Assessing Contractor Implementation of Cybersecurity Requirements, consistent with .
DoD has determined the following conditions have been met:
a. The collection of information is needed prior to the expiration of time periods normally associated with a routine submission for review under the provisions of the PRA, to enable the Department to immediately begin assessing the current status of contractor implementation of NIST SP 800-171 on their information systems that process CUI.
Upon publication of this rule, DoD intends to provide a separate 60-day notice in the Federal Register requesting public comment for OMB Control Number 0750-0004, Assessing Contractor Implementation of Cybersecurity Requirements.
DOD estimates the annual public reporting burden for the information collection as follows:
Read Also: Government Jobs Sacramento
Also Check: Las Vegas Rtc Jobs
New Nist Security Standards For Federal Contractors
There’s a new set of rules for companies seeking federal government contract work. After months of drafts and public comments, the National Institute of Standards and Technology the final SP 800-171A, Assessing Security Requirements for Controlled Unclassified Information. This allows companies to determine if they’re in compliance with requirements for handling controlled unclassified information.
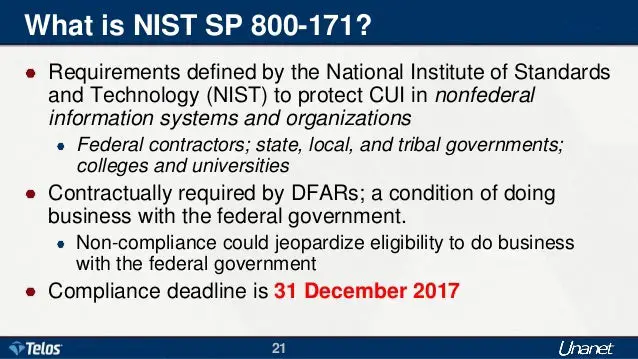
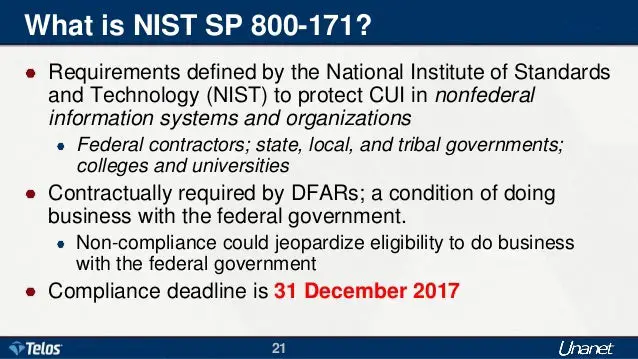
What Is The Purpose Of Nist 800
The cybersecurity requirements within NIST 800-171 are designed to safeguard CUI in the IT networks of government contractors and subcontractors. It defines the practices and procedures that government contractors must adhere to when their networks process or store CUI. NIST 800-171 only applies to those parts of a contractors network where CUI is present.
Top tip for NIST 800-171 compliance: Conducting evidence-based assessments are going to be key to accurately determining an organizations NIST 800-171 compliance. An organization should maintain an up-to-date System Security Plan as well as have policies and practices in place that can be used to demonstrate and evidence compliance.
Read Also: Free Dental Implants Grants
A Case For Moving To The Cloud
Implementing the NIST 800-171 framework is a big job. It will take more than one person to do it and it might change the way you do business, says Austin. You may need to change your hardware requirements, for example. But in order to do business under stringent governmental regulations and guidelines, they’re necessary actions.
That’s why many contractors today are scaling their operations by moving to hosted cloud construction and business management solutions that have many of these cybersecurity protections built in.
Real-Life Story
Internal Penetration Tests And Vulnerability Scans
Perform regular penetration tests and look for chains of vulnerability that could lead to a big hack. Assume a user clicked a bad link, Austin suggests, and follow that path to see what a bad guy can do with that.
Additionally, monthly vulnerability scans can tell you a lot about the care and feeding of your network.
Also Check: City Of Los Lunas Jobs
A Govt Contractors Road Map To Biden Cybersecurity Order
This will affect developers, resellers and users of software extending well into the commercial marketplace.
WhenFollowing input from industry in the coming months, expect new NIST guidelines on software supply chain security by November within 180 days of the executive order. Throughout this summer, expect significant attention to key definitions and standards, including the definition of critical software.Within one year of the executive order mid-May 2022 designated agencies shall recommend to the FAR Council new rules regarding software security, including certification requirements. And following these FAR amendments, agencies shall begin the removal of noncompliant software for purchase by federal agencies.There can be little doubt that this executive order is an ambitious use of executive power to address a serious and continuing threat to our national security. While the devil is in the details, and the rollout will take some time, government contractors and their suppliers should plan ahead and take advantage of the opportunity to evaluate their exposure, comment on the rulemaking, and prepare to bring to bear the resources they will need to operate in a new compliance environment.
A Govt Contractors Road Map to Biden Cybersecurity Order, by Justin A. Chiarodo and Sharon R. Klein, was published in Law360 on June 11, 2021.
Nist Proposes Enhanced Security Requirements For Certain Government Contractors
The National Institute of Standards and Technology has announced proposed changes to NIST Special Publication 800-171, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations. The proposed changes are twofold: making minor editorial changes and clarifications to existing SP 800-171, and proposing enhanced security requirements for critical programs and high value assets to protect against the advanced persistent threat in a new publication, SP 800-171B. These proposals will not only affect the government contractors who are directly subject to the requirements through their agreements with the government, but may also ripple into the private sector. These proposals are open for public comment through August 2, 2019*.
Originally published in 2015, the NIST SP 800-171 controls are designed to set minimal security standards for government contractors that process, store, or transmit controlled unclassified information . The types of information that are considered CUI are listed in the CUI Registry and includes a wide range of information, from federal taxpayer information to critical defense information. The proposed revisions to SP 800-171, Revision 2 are minor editorial changes no changes were proposed to the basic or derived security requirements. NIST has stated that a comprehensive update to SP 800-171 will be forthcoming in Revision 3.
Don’t Miss: Mortgage Stimulus Program For Middle Class 2021
The Daily Journal Of The United States Government
Legal Status
This site displays a prototype of a Web 2.0 version of the daily Federal Register. It is not an official legal edition of the Federal Register, and does not replace the official print version or the official electronic version on GPOs govinfo.gov.
The documents posted on this site are XML renditions of published Federal Register documents. Each document posted on the site includes a link to the corresponding official PDF file on govinfo.gov. This prototype edition of the daily Federal Register on FederalRegister.gov will remain an unofficial informational resource until the Administrative Committee of the Federal Register issues a regulation granting it official legal status. For complete information about, and access to, our official publications and services, go to About the Federal Register on NARA’s archives.gov.
Legal Status
| Consists of the 15 basic safeguarding requirements from FAR clause 52.204-21. | |
| 2 | Consists of 65 security requirements from NIST SP 800-171 implemented via DFARS clause 252.204-7012, 7 CMMC practices, and 2 CMMC processes. Intended as an optional intermediary step for contractors as part of their progression to Level 3. |
| 3 | Consists of all 110 security requirements from NIST SP 800-171, 20 CMMC practices, and 3 CMMC processes. |
| 4 | Consists of all 110 security requirements from NIST SP 800-171, 46 CMMC practices, and 4 CMMC processes. |
| 5 | Consists of all 110 security requirements from NIST SP 800-171, 61 CMMC practices, and 5 CMMC processes. |
New Cyber Guidelines Out For Government Contractors
Sign up for our newsletter.
NOTE: This story first appeared on FCW.com.
Its no secret that foreign nations have recognized that one of the best pathways to hacking and stealing U.S. government technology is by targeting its industrial base. Foreign countries are targeting and compromising U.S. contractors so frequently that the Department of Defense asked the National Institute of Standards and Technology to develop custom security guidance to address the problem.
A draft version of that new guidance publicly released June 19 lays out 31 new recommendations for contractors to harden their defenses and protect unclassified government data that resides on their networks from advanced persistent threats or government-sponsored hackers. Such data can range from Social Security numbers and other personally identifying information to critical defense program details.
The recommendations include processes like implementing dual-authorization access controls for critical or sensitive operations, employing network segmentation where appropriate, deploying deception technologies and establishing or employing threat-hunting teams and a security operations center to continuously monitor system and network activity.
In addition to the NIST guidelines, DOD has also taken steps to beef up participation in information sharing programs and rolled out new cybersecurity certification standards for its contractor base in recent months.
Manage Consent Preferences
Read Also: Federal Jobs Las Vegas
What To Do If A Security Breach Occurs
According to US-CERT Federal Incident Notification Guidelines, FISMA requires federal Executive Branch civilian agencies to notify and consult with US-CERT regarding information security incidents involving their information and information systems, whether managed by a federal agency, contractor, or other source. The Notification Requirement states that incidents must be reported within one hour of being identified by the agencys top-level Computer Security Incident Response Team , Security Operations Center , or information technology department. In some cases, it may not be feasible to have complete and validated information for the section below prior to reporting. Agencies should provide their best estimate at the time of notification and report updated information as it becomes available. Incidents can be submitted via the US-CERT Incident Reporting System.
New Cybersecurity Requirements For Government Contractors
Effective June 15, 2016, a new rule recently published by the US Department of Defense , General Services Administration , and National Aeronautics and Space Administration will require federal government contractors to apply 15 basic cybersecurity safeguarding requirements and procedures to protect their information systems. All safeguarding requirements are based on security requirements published in the National Institute of Standards and Technologys Special Publication 800-171, Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations.
Read Also: Los Lunas City Jobs
How Does Nist 800
The main effect that NIST 800-172 has on contractors is an added layer of protection for those who need it. Contractors who are unlikely to be directly targeted by APT wont be affected at all by 800-172 since it will likely only apply to contracts that are considered high risk and must defend against APT.
Iii Applicability To Contracts At Or Below The Simplified Acquisition Threshold And For Commercial Items Including Commercially Available Off
This rule creates the following new solicitation provision and contract clauses:
- DFARS 252.204-7019, Notice of NIST SP 800-171 DoD Assessment Requirements
- DFARS clause 252.204-7020, NIST SP 800-171 DoD Assessment Requirements and
- DFARS clause 252.204-7021, Cybersecurity Maturity Model Certification Requirements.
The objective of this rule is provide the Department with: The ability to assess contractor implementation of NIST SP 800-171 security requirements, as required by DFARS clause 252.204-7012, Safeguarding Covered Defense Information and Cyber Incident Reporting and assurances that DIB contractors can adequately protect sensitive unclassified information at a level commensurate with the risk, accounting for information flowed down to subcontractors in a multi-tier supply chain. Flowdown of the requirements is necessary to respond to threats that reach even the lowest tiers in the supply chain. Therefore, to achieve the desired policy outcome, DoD intends to apply the new provision and clauses to contracts and subcontracts for the acquisition of commercial items and to acquisitions valued at or below the simplified acquisition threshold, but greater than the micro-purchase threshold. The provision and clauses will not be applicable to contracts or subcontracts exclusively for the acquisition of commercially available off-the-shelf items.
You May Like: Dental Implants Grant
What Is Nist Compliance
Companies that provide products and services to the federal government need to meet certain security mandates set by NIST. Specifically, NIST Special Publication 800-53 and NIST Special Publication 800-171 are two common mandates with which companies working within the federal supply chain may need to comply.
The first draft of NIST Special Publication 800-171 Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations, was actually created in May 2015.
This original document was intended to provide guidance for non-federal organizations looking to protect sensitive unclassified federal information that was housed in their own information systems and environments. It clarified their role in data breach incidents and provided guidance on the types of data to protect and the kinds of protections to apply.
The latest version of this document is NIST SP 800-171 Rev2 which was last updated February 2020.
C Description Of And Estimate Of The Number Of Small Entities To Which The Rule Will Apply
This rule will impact all small businesses that do business with Department of Defense, except those competing on contracts or orders that are exclusively for COTS items or receiving contracts or orders valued at or below the micro-purchase threshold.
1. The NIST SP 800-171 DoD Assessment Methodology
According to data available in the Electronic Data Access system for fiscal years 2016, 2017, and 2018, on an annual basis DoD awards on average 485,859 contracts and orders that contain DFARS clause 252.204-7012 to 39,204 unique awardees, of which 262,509 awards are made to 26,468 small entities . While there may be some entities that have contracts that contain the clause at 252.204-7012, but never process CUI and, therefore, do not have to implement NIST SP 800-171, it is not possible for DoD to estimate what fraction of unique entities fall into this category. Assuming all of these small entities have covered contractor information systems that are required to be in compliance with NIST SP 800-171, then all of these entities would be required to have, at minimum, a Basic Assessment in order to be considered for award.
| Assessment | |
|---|---|
| 81 | 81 |
2. The CMMC Framework
| Year | |
|---|---|
| 33 | 163,391 |
Don’t Miss: Clark County Nevada Government Jobs
Who Performs A Compliance Assessment
This is a self assessment the SSP and POA& M are your documents.
While the government can ask for copies, they are intended to help you identify and manage risk and better protect your and the governments information. Ntiva has assisted dozens of companies perform the risk assessment and document the results.
